Top 4 Access Control Credentials
Physical credentials, such as ID cards and key fobs, have long been the backbones of access control. These tangib le tokens offer immediate visual verification and are generally user-friendly. Many employees appreciate the simplicity of tapping or swiping a card to gain entry. Moreover, these credentials can often serve double duty, functioning as company ID badges or even integrating with time and attendance systems. However, physical credentials aren’t without their drawbacks. They can be lost, stolen, or shared, potentially compromising security. The cost of replacing lost cards and managing inventory can add up over time. Additionally, in our increasingly digital world, carrying an extra item might be seen as cumbersome by some users.
le tokens offer immediate visual verification and are generally user-friendly. Many employees appreciate the simplicity of tapping or swiping a card to gain entry. Moreover, these credentials can often serve double duty, functioning as company ID badges or even integrating with time and attendance systems. However, physical credentials aren’t without their drawbacks. They can be lost, stolen, or shared, potentially compromising security. The cost of replacing lost cards and managing inventory can add up over time. Additionally, in our increasingly digital world, carrying an extra item might be seen as cumbersome by some users.
\n
PIN-based systems offer the advantage of not requiring any physical object. They’re cost-effective to implement and can be easily changed if compromised. For users, there’s no risk of forgetting or losing a card. PIN systems can also be ideal for temporary access, such as for contractors or visitors. On the flip side, PINs can be forgotten, shared, or observed by unauthorized individuals. There’s also the risk of ‘shoulder surfing,’ where someone watches as the code is entered. To mitigate these risks, many organizations use PINs in combination with other credential types for multi-factor authentication.
\n
Biometric systems, using fingerprints, retinal scans, or facial recognition, offer a high level of security. They’re difficult to forge and can’t be lost or forgotten like physical cards or PINs. Biometrics also provide a clear audit trail, as they’re linked directly to individuals rather than objects that could be shared. However, biometric systems can be expensive to implement and may raise privacy concerns among users. They can also face challenges in certain environments – for instance, fingerprint scanners may struggle with dirty or worn fingerprints in industrial settings.
\n
Mobile credentials, which turn smartphones into access devices, are gaining popularity. They offer convenience – most people always have their phones with them – and can be u pdated or revoked remotely. Mobile credentials can also integrate with other smartphone functions, potentially streamlining processes beyond just access control. The downsides include the
pdated or revoked remotely. Mobile credentials can also integrate with other smartphone functions, potentially streamlining processes beyond just access control. The downsides include the 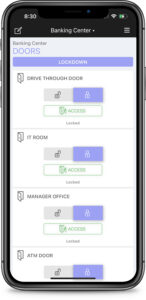 need for compatible infrastructure and the reliance on users’ personal devices. There are also concerns about battery life and what happens if a phone is lost or stolen. However, many of these issues can be mitigated with proper policies and backup systems.
need for compatible infrastructure and the reliance on users’ personal devices. There are also concerns about battery life and what happens if a phone is lost or stolen. However, many of these issues can be mitigated with proper policies and backup systems.
\n
Smart cards represent a step up in security from traditional proximity cards. They use encryption to protect data transmission, making them much harder to clone or hack. Smart cards can also store additional information, potentially serving multiple functions beyond access control. The primary drawbacks of smart cards are higher costs compared to simpler card technologies and the need for compatible readers. However, their enhanced security features often justify the investment for many organizations.
\n
When selecting an access control credential system, consider your organization’s specific needs. High-security environments might prioritize the robust protection of biometrics or encrypted smart cards. Companies with a mobile-first culture might lean towards smartphone-based solutions. Organizations with high turnover or frequent visitors might find the flexibility of PIN systems appealing.
\n
It’s also worth considering hybrid systems. Many modern access control setups allow for multiple credential types, offering the flexibility to use different solutions for different areas or user groups within the same organization.
\nAs your business grows and evolves, so do these access control credentials. Regular updates and integrations with other smart devices ensure that your security system remains cutting-edge and adaptable to your changing needs. If you have questions about how our access control credential solutions can benefit your business, please do not hesitate to contact us at info@verifiedsecurity.com.\n\n-Scott Hightower, Verified Security“}]}],”section_settings”:””},”scripts”:{},”css”:{},”css_page”:””,”template_setting”:{“settings”:{“id”:”settings”}},”template_setting_top”:{},”page_setting”:{“settings”:[“lock-mode-off”]},”post_type_setting”:{“settings”:{“image”:”https://verifiedsecurity.com/wp-content/uploads/2024/07/DMP_Access_33.jpg|450|800|999956868″,”excerpt”:””,”extra_1″:””,”extra_2″:””,”icon”:{“icon”:””,”icon_style”:””,”icon_image”:””}}}}
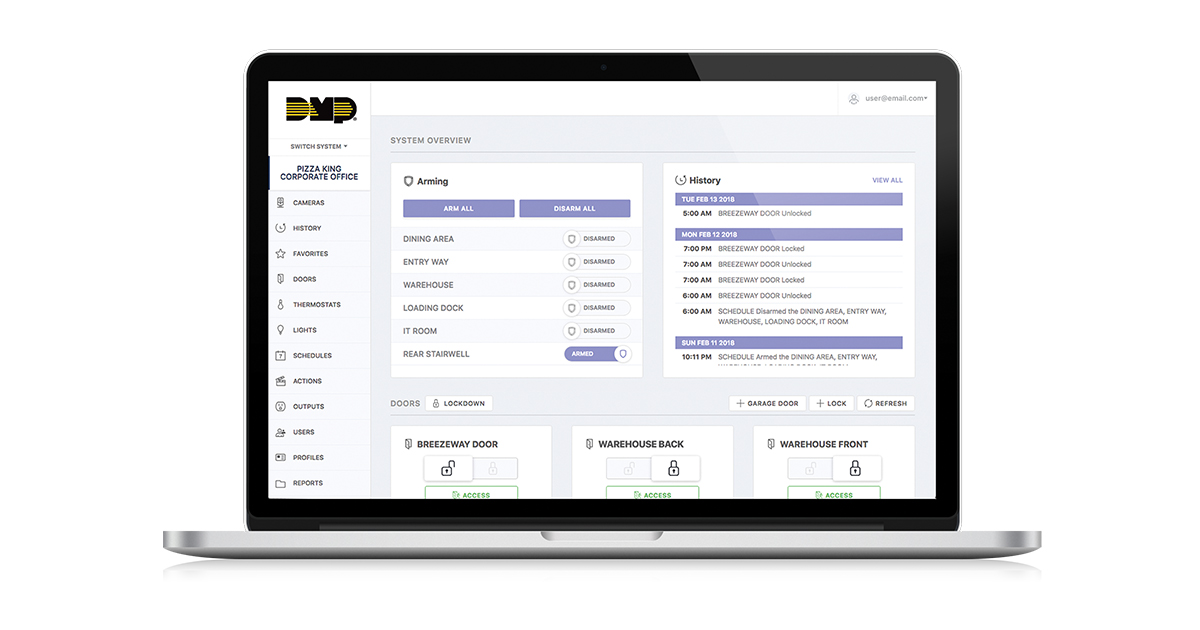
]]>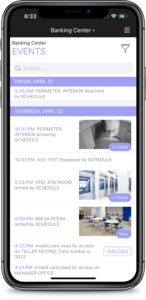 ct and Virtual Keypad, you can arm or disarm your system, lock or unlock doors, and view onsite video—all from your smartphone. This level of control ensures that you’re always connected to your business, providing peace of mind and enhancing operational efficiency.\n\nRemote access capabilities provide real-time insights that can drive smarter business decisions. Receive instant notifications about employee arriva
ct and Virtual Keypad, you can arm or disarm your system, lock or unlock doors, and view onsite video—all from your smartphone. This level of control ensures that you’re always connected to your business, providing peace of mind and enhancing operational efficiency.\n\nRemote access capabilities provide real-time insights that can drive smarter business decisions. Receive instant notifications about employee arriva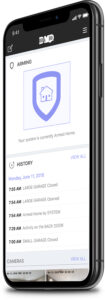 ls and departures, unexpected entries, or changes in environmental conditions. This immediate awareness allows you to respond quickly to any situation, improving both security and operational effectiveness.\n\nFor businesses with multiple locations, remote access is a game-changer. Manage security for all your properties from a single app, ensuring consistent security practices across your organization while saving time and resources.\n\nThese systems also enhance emergency response capabilities. In case of an alarm, monitoring centers are automatically alerted, ensuring rapid response from emergency services if needed. You’ll be notified immediately, allowing you to assess the situation and provide additional information to responders.\n\nAs your business grows and evolves, so do these remote access solutions. Regular updates and integrations with other smart devices ensure that your security system remains cutting-edge and adaptable to your changing needs. If you have questions about how our remote access security solutions can benefit your business, please do not hesitate to contact us at info@verifiedsecurity.com.\n\n-Scott Hightower, Verified Security“}]}],”section_settings”:””},”scripts”:{},”css”:{},”css_page”:””,”template_setting”:{“settings”:{“id”:”settings”}},”template_setting_top”:{},”page_setting”:{“settings”:[“lock-mode-off”]},”post_type_setting”:{“settings”:{“image”:”https://verifiedsecurity.com/wp-content/uploads/2024/07/AprilSocial18_7-1024×538.jpg|630|1200|999956859″,”excerpt”:””,”extra_1″:””,”extra_2″:””,”icon”:{“icon”:””,”icon_style”:””,”icon_image”:””}}}}
]]>
ls and departures, unexpected entries, or changes in environmental conditions. This immediate awareness allows you to respond quickly to any situation, improving both security and operational effectiveness.\n\nFor businesses with multiple locations, remote access is a game-changer. Manage security for all your properties from a single app, ensuring consistent security practices across your organization while saving time and resources.\n\nThese systems also enhance emergency response capabilities. In case of an alarm, monitoring centers are automatically alerted, ensuring rapid response from emergency services if needed. You’ll be notified immediately, allowing you to assess the situation and provide additional information to responders.\n\nAs your business grows and evolves, so do these remote access solutions. Regular updates and integrations with other smart devices ensure that your security system remains cutting-edge and adaptable to your changing needs. If you have questions about how our remote access security solutions can benefit your business, please do not hesitate to contact us at info@verifiedsecurity.com.\n\n-Scott Hightower, Verified Security“}]}],”section_settings”:””},”scripts”:{},”css”:{},”css_page”:””,”template_setting”:{“settings”:{“id”:”settings”}},”template_setting_top”:{},”page_setting”:{“settings”:[“lock-mode-off”]},”post_type_setting”:{“settings”:{“image”:”https://verifiedsecurity.com/wp-content/uploads/2024/07/AprilSocial18_7-1024×538.jpg|630|1200|999956859″,”excerpt”:””,”extra_1″:””,”extra_2″:””,”icon”:{“icon”:””,”icon_style”:””,”icon_image”:””}}}}
]]> <\/a>\n\nBased on the triggers you choose, you can initiate actions such as sending a notification or activating a device like a siren or a flashing strobe light.\n\nHow might this benefit you? Would you like to know if someone has propped open a security door that is supposed to stay closed? Or, would you like to know if someone attempted to use an invalid card at one of your card readers? These are just two examples of the many options you can select when setting up rules for Maxpro Cloud.\n\nMaxpro Cloud was designed to be easy to use and flexible to give you the most options for managing the security and access control of your facilities. If you have questions about your options for access control and security, please do not hesitate to contact us at info@verifiedsecurity.com.<\/a>\n\n-Scott Hightower, Verified Security<\/a>“}]}],”section_settings”:””},”scripts”:[],”css”:[],”css_page”:””,”template_setting”:{“settings”:{“id”:”settings”}},”template_setting_top”:[],”page_setting”:{“settings”:[“lock-mode-off”]},”post_type_setting”:{“settings”:{“image”:”https:\/\/verifiedsecurity.com\/wp-content\/uploads\/2018\/04\/HSF-MPC-Landing-Page-Thumbs-case-study-general.jpg|284|535|999956004″,”excerpt”:””,”extra_1″:””,”extra_2″:””,”icon”:{“icon”:””,”icon_style”:””,”icon_image”:””}}}}
]]>
<\/a>\n\nBased on the triggers you choose, you can initiate actions such as sending a notification or activating a device like a siren or a flashing strobe light.\n\nHow might this benefit you? Would you like to know if someone has propped open a security door that is supposed to stay closed? Or, would you like to know if someone attempted to use an invalid card at one of your card readers? These are just two examples of the many options you can select when setting up rules for Maxpro Cloud.\n\nMaxpro Cloud was designed to be easy to use and flexible to give you the most options for managing the security and access control of your facilities. If you have questions about your options for access control and security, please do not hesitate to contact us at info@verifiedsecurity.com.<\/a>\n\n-Scott Hightower, Verified Security<\/a>“}]}],”section_settings”:””},”scripts”:[],”css”:[],”css_page”:””,”template_setting”:{“settings”:{“id”:”settings”}},”template_setting_top”:[],”page_setting”:{“settings”:[“lock-mode-off”]},”post_type_setting”:{“settings”:{“image”:”https:\/\/verifiedsecurity.com\/wp-content\/uploads\/2018\/04\/HSF-MPC-Landing-Page-Thumbs-case-study-general.jpg|284|535|999956004″,”excerpt”:””,”extra_1″:””,”extra_2″:””,”icon”:{“icon”:””,”icon_style”:””,”icon_image”:””}}}}
]]>